For a long time you can create console sessions to your VM and BM compute instances in OCI. This is a remote KVM method like HP iLO or dell DRAC. Not relying on networking you can still connect to your instance. Traditionally to enable a remote console session, you had to setup a SSH tunnel and via that tunnel to an serial or VNC session.
NEW in OCI: Embedded Serial Console session direct from the OCI Web portal.
You can just go to any of your Linux based instances and launch the Cloud Shell – Console Connection. After the console session is created you will get a direct login prompt to your instance.
What is the password problem?!?!
So you now want to login to your instance… but what is the default password for the opc or ubuntu users?? Well there is none! OCI creates user accounts based on SSH key pairs not based on passwords. So while you know have easy access to the console, you still would not be able to login.
Create backdoor user when creating new instances
One way to solve this, is to add some cloud-init scripting that a backdoor user is created with a password. This does not modify anything about the SSH setup. Meaning connecting over SSH to you instance can still only be done using an SSH key pair. This “backdoor” is therefor only accessible using the remote console option.
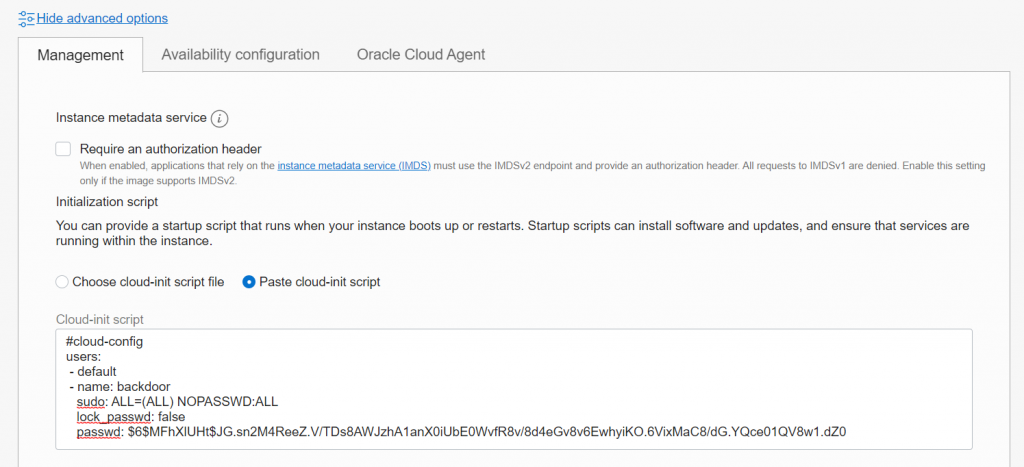
When you create a new Linux instance in OCI, at the bottom click on the “Show advanced option” link. A new section will pop up where you can specify or a cloud-init file or paste a cloud-init script. Click on the Paste cloud-init script and paste the below script in this field
#cloud-config
users:
- default
- name: backdoor
sudo: ALL=(ALL) NOPASSWD:ALL
lock_passwd: false
passwd: $6$MFhXlUHt$JG.sn2M4ReeZ.V/TDs8AWJzhA1anX0iUbE0WvfR8v/8d4eGv8v6EwhyiKO.6VixMaC8/dG.YQce01QV8w1.dZ0The above script will create the normal default users and a new user called backdoor. This user will not have an SSH key pair, so you will NOT be able to login via SSH as this user. The user does have a password setup. This password is an linux encrypted password in the scipt. The actual password is: 1LoveOracle!!
When you now create an instance with this cloud init script, you will be able to login using this backdoor user.
How secure is this?
So I am not claiming to be a security expert, so please evaluate this option with your security people 🙂
- You can only use this backdoor user via the serial console or after people are logged in via SSH as a different user. They can use the su command to switch to the backdoor user (if they know the password).
- If you are really going to use this, please create a Linux encrypted password yourself. So you only know the real password!
If you know a lot more about security and think this is really a dumb thing to configure, please leave a comment!
You can find the Windows and Linux cloud init scripts also on my github page:
https://github.com/AnykeyNL/OCI-Cloudinit-Backdoors
you login in with your shell if you set the key at the beginning and do sudo passwd USERNAME and it will prompt you to change the password
perfect thanks man
Great tip, could we make this work in existent instances ?
thanks
This is valid in 2022?
yes
Thank you. Great idea!!!
The password is 1LoveOracle!! or 1LoveOracle ?
I’m trying all 2 ways but I can’t login to Cloud Shell
You can’t copy paste the password into the console session, you need to type it in manually.
Command to generate your linux encrypted password is mkpasswd -m sha512crypt
Very nice. this post saves me.
If instance has been created, how to add the similar backdoor user?
You would have to login to the instance first and manually create an user with a password.